CVE-2026-39349 - Use of AES-ECB for Sensitive Data Encryption Enables Pattern Disclosure in OrangeHRM
Author and Researcher

Ravindu Wickramasinghe
@rvz
1. Description
OrangeHRM Open Source encrypts sensitive application data using Rijndael/AES in ECB mode in src/plugins/orangehrmCorePlugin/Utility/Cryptographer.php. ECB is deterministic - identical plaintext values always produce identical ciphertext. An attacker with database access can correlate repeated ciphertext values and infer salary patterns, identify repeated SSNs, and recognize reused credentials without ever decrypting a single value.
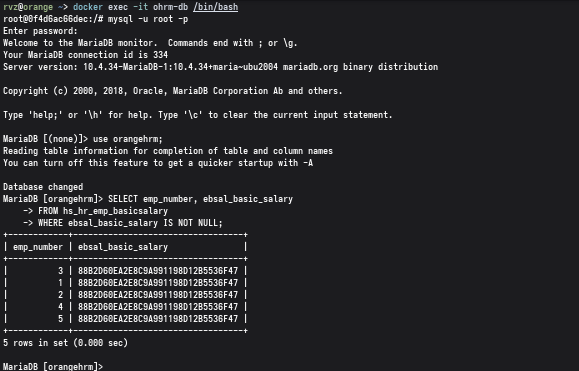
Direct testing of the Cryptographer class confirms identical ciphertext output for repeated salary inputs. Database inspection shows employees with the same salary share identical encrypted values in hs_hr_emp_basicsalary.ebsal_basic_salary. The same encryption logic is applied across SSNs, SMTP passwords, LDAP bind credentials, and OAuth secrets. Because ECB provides no integrity protection, encrypted values can also be copied across records to manipulate sensitive fields without knowledge of the key.
Affected versions: OrangeHRM >= 5.0, <= 5.8
Patched version: 5.8.1
2. ECB Mode - Why It Fails
ECB (Electronic Codebook) encrypts each block independently with the same key. No initialization vector is used, no block is chained to the previous one. The consequence is straightforward: feed in the same 16-byte plaintext block twice, get the same ciphertext block twice. For structured data like salaries and SSNs - where values repeat across employees - this turns the encrypted column into a frequency table. An attacker doesn't need the key. They need the ciphertext and basic knowledge of the data domain.
The absence of authentication means ciphertext is also malleable. Copy the encrypted salary from one employee record to another, and the application decrypts it without complaint. No MAC, no AEAD, no integrity check of any kind.
3. Source Code Analysis
The vulnerable encryption implementation resides in src/plugins/orangehrmCorePlugin/Utility/Cryptographer.php. The class uses openssl_encrypt() with the AES-256-ECB cipher, producing deterministic output for any given plaintext and key pair. This method is called for all sensitive field encryption across the application - salary data, identity numbers, and stored credentials share the same flawed primitive.
4. Steps to Reproduce
- Log in with administrative privileges.
- Create multiple employees and assign each the same salary value.
- Query the database:terminal
SELECT emp_number, ebsal_basic_salaryFROM hs_hr_emp_basicsalaryWHERE ebsal_basic_salary IS NOT NULL; - All employees with the same salary produce identical ciphertext values, confirming ECB mode leakage. Group by the encrypted column to identify salary clusters without decryption.
5. Impact
- Salary pattern inference - identical ciphertext reveals which employees share the same compensation without decrypting any value.
- SSN correlation - repeated SSN ciphertext identifies duplicate or shared identity numbers across records.
- Credential reuse detection - identical encrypted SMTP or LDAP passwords expose credential sharing across configurations.
- Ciphertext manipulation - absence of integrity protection allows copying encrypted values between records to silently alter salary, SSN, or credential fields.
6. CVSS
CVSS 4.0 Score: 2.1 (Low)
CVSS:4.0/AV:N/AC:H/AT:P/PR:H/UI:N/VC:L/VI:N/VA:N/SC:N/SI:N/SA:N
7. Recommendations
Replace ECB with an authenticated encryption mode such as AES-256-GCM to provide both confidentiality and integrity. If GCM cannot be adopted immediately, use AES-256-CBC with a cryptographically secure per-record IV and protect the IV and ciphertext with HMAC-SHA256. Keys must be generated using a secure RNG and support versioning for future rotation.
Existing encrypted values should be decrypted using the current routine and re-encrypted using the new scheme during a controlled maintenance process. Prioritize sensitive fields: salary data, identity information, and stored credentials.